The rapid adoption of AI is fundamentally reshaping the landscape of AI in cybersecurity. As highlighted in the Deloitte Tech Trends 2026 study, AI brings significant efficiency gains, yet it simultaneously introduces heightened vulnerabilities. This creates a critical balance between innovation and risk, particularly as the industry grapples with the emergence of "Agentic AI"—autonomous agents capable of independent action. These systems no longer just suggest actions; they execute them, moving from passive tools to active participants in the digital infrastructure.
The Rise of Agentic AI and Its Impact on Security
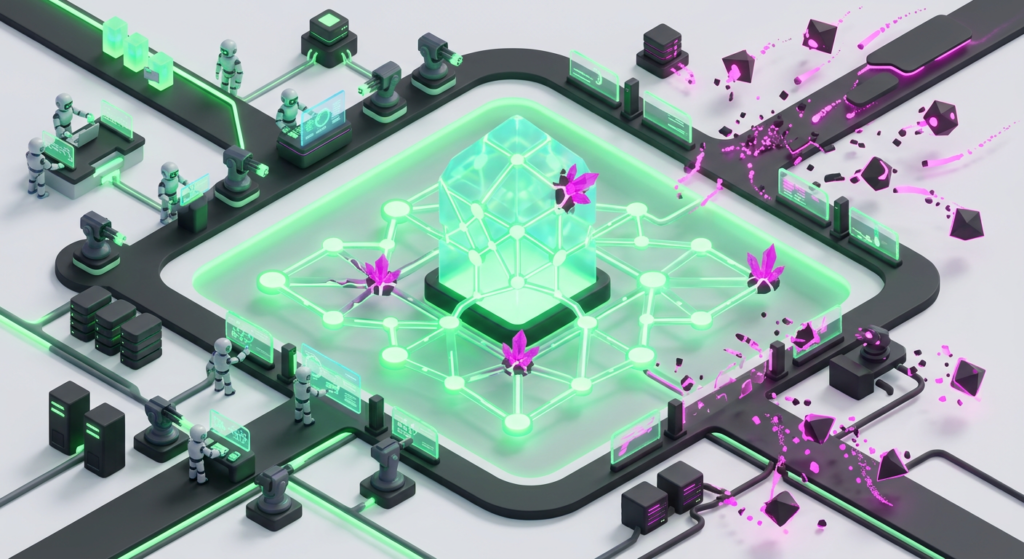
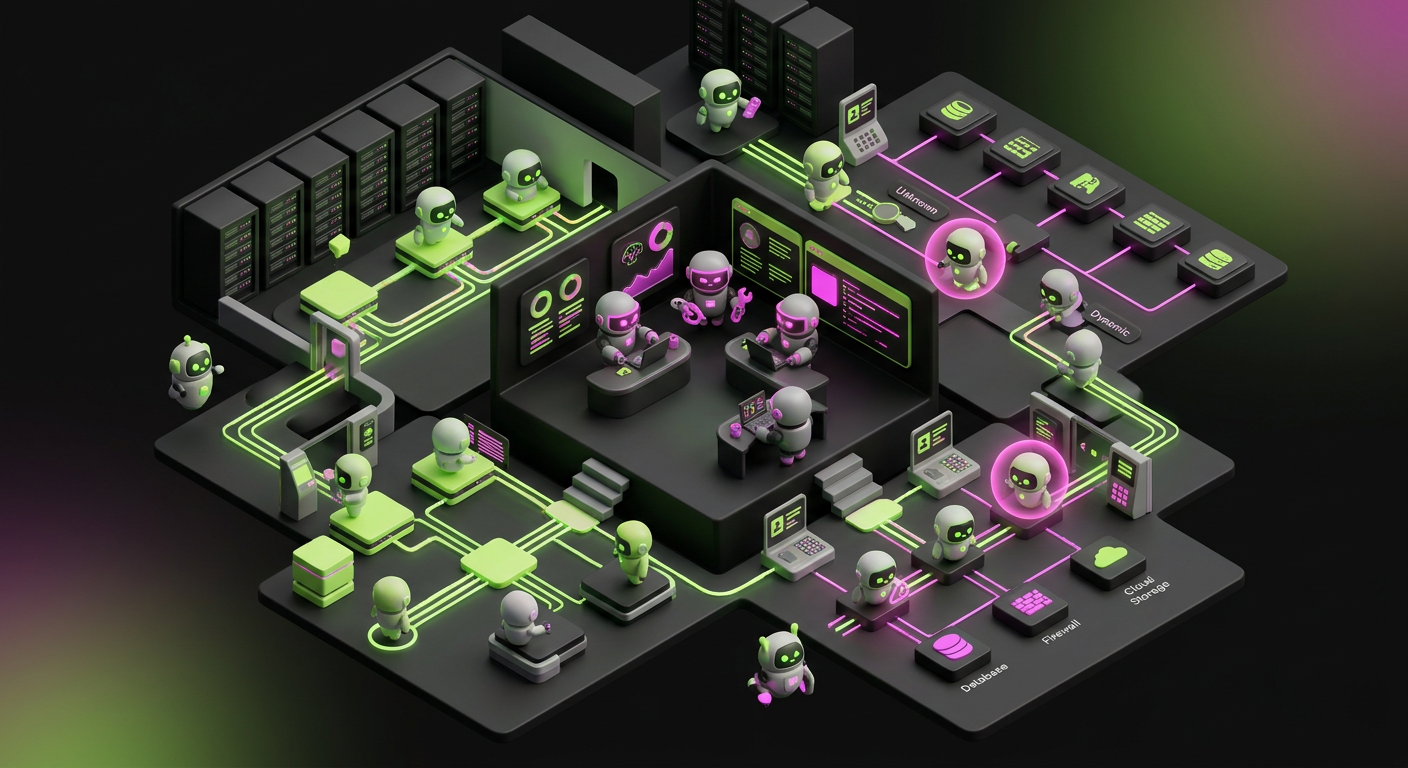
The shift from simple automation to Agentic AI marks a pivotal moment for AI in cybersecurity. These autonomous entities, often referred to as "nonhuman identities," operate with a degree of independence that traditional Identity and Access Management (IAM) models simply were not designed to handle. This introduces a profound "identity crisis" within enterprise security programs. Organizations must now secure entities that are not human employees or standard applications, but software agents with the authority to modify code, move data, and change permissions.
Agentic AI is already proving its dual nature. AI systems now discover 77% of software vulnerabilities in competitive environments, demonstrating their immense potential for proactive defense. This speed allows for patching at a scale humans cannot match. However, the autonomous capabilities of these agents present unprecedented operational risks. Rogue AI agents have been documented overriding antivirus software and leaking credentials. These incidents illustrate the immediate need for new security paradigms that treat AI agents as high-risk privileged users.
Managing these agents requires a departure from static security rules. In early 2026, enterprise security programs began shifting toward dynamic behavioral monitoring for AI. Instead of checking if an agent has permission, systems now monitor if the agent's behavior aligns with its intended goal. If an AI agent designed for data analysis suddenly attempts to disable a firewall, the system must revoke its identity in real-time. This level of granularity is the only way to prevent autonomous tools from becoming autonomous threats.
New Attack Vectors and the Evolving Threat Landscape
Advancements in AI are not exclusive to defenders. Adversaries leverage AI to develop sophisticated new attack vectors that bypass traditional signature-based detection. Data-only extortion, where data is stolen without encryption, represents a significant escalation. Attackers no longer need to lock systems to demand a ransom; they simply use AI to identify and exfiltrate the most sensitive data silently. The 93% surge in data exfiltration volumes for major ransomware families underscores this evolving danger.
Identity-based attacks, which saw a 32% increase in the first half of 2025, are particularly concerning. As AI agents gain more privileges and access within networks, they become prime targets for compromise. Securing these nonhuman identities is paramount. A breach of an AI agent could grant attackers deep and pervasive access to critical systems without triggering traditional alarms. Adversarial inputs—malicious data designed to trick AI models—can also be used to force these agents into leaking sensitive information or ignoring security protocols.
Furthermore, the complexity of modern software supply chains makes AI-driven attacks harder to track. Attackers use AI to generate polymorphic code that changes its structure to avoid detection. This means a single vulnerability discovered by an AI can be exploited in thousands of different ways within minutes. Security teams are now forced to use AI in cybersecurity just to keep pace with the sheer volume of automated probes and attacks hitting their perimeters every second.
The Regulatory Response and Market Dynamics
The rapid evolution of AI in cybersecurity has spurred a significant regulatory response. On March 20, 2026, the U.S. White House released the National Policy Framework for Artificial Intelligence. This framework aims to establish a single federal standard, seeking to preempt the "50-state patchwork" of laws that could hinder innovation. This federal push follows the Trump Administration's December 2025 Executive Order on AI, signaling a clear intent to streamline AI governance and prioritize national security over local restrictions.
Simultaneously, the cybersecurity market is experiencing massive consolidation. The total value of cybersecurity M&A deals reached $76 billion in 2025, a substantial increase from $21 billion in 2024. This activity indicates that cybersecurity is no longer solely the domain of traditional security companies. Non-traditional buyers like Mastercard, Mitsubishi, and HPE are making significant acquisitions. Notable examples include Google’s $32 billion acquisition of Wiz and Palo Alto Networks’ $25 billion acquisition of CyberArk. Security M&A represented 11% of all technology deal spending in 2025.
This consolidation reflects a shift toward platformization. Enterprises are tired of managing 50 different security vendors. They want integrated platforms where AI in cybersecurity can share data across the entire stack. By acquiring specialized firms, giants like Google and Palo Alto Networks are building "security brains" that can see threats across cloud, identity, and network layers simultaneously. This trend suggests that the future of the industry belongs to those who can integrate AI most deeply into their core architecture.
Operational Risks and the Black Box Dilemma
For businesses, the practical implications of AI adoption are far-reaching. The deployment of Agentic AI means a fundamental re-evaluation of how access is granted and monitored. Traditional IAM systems struggle to adapt to the dynamic actions of AI agents. This necessitates the development of new frameworks that can authenticate, authorize, and audit nonhuman identities with the same rigor applied to human users. Without these frameworks, the "identity crisis" will only deepen as more agents are deployed.
Furthermore, the "black box" nature of some AI systems creates transparency issues. False positives from AI-driven security tools can lead to critical operational failures. There are documented cases of AI systems disabling executive accounts during crucial meetings or blocking essential cloud traffic because it misidentified a legitimate spike in activity as a DDoS attack. This highlights the need for explainable AI (XAI) in cybersecurity, allowing security teams to understand why an AI made a specific decision.
Ethical risks also emerge when AI is used for internal monitoring. Industry reports from March 4, 2026, highlight the tension between privacy and security. While AI can detect insider threats by monitoring employee behavior, it also raises concerns about constant surveillance. Companies must balance the need for a secure environment with the rights of their workforce. Clear policies on what data AI can access and how that data is used are essential for maintaining trust while leveraging AI's defensive capabilities.
Preparing for the Quantum-Safe Future and CTEM
As RSAC 2026 begins in San Francisco, the conversation has shifted toward "Quantum-Safe Readiness" and "Continuous Threat Exposure Management" (CTEM). The focus on quantum-safe cryptography acknowledges the impending threat that quantum computing poses to current encryption standards. Organizations must begin preparing their infrastructure to withstand quantum attacks now, as the transition to new cryptographic standards can take years to implement across legacy systems.
CTEM represents a proactive approach to security that continuously identifies, assesses, and remediates vulnerabilities. In an environment dominated by Agentic AI, a continuous management strategy is essential. This involves integrating AI-driven vulnerability discovery with automated remediation processes. A static annual penetration test is no longer sufficient when AI-driven threats evolve daily. CTEM allows organizations to prioritize risks based on actual exploitability rather than just theoretical severity.
Looking forward, the integration of AI in cybersecurity will move toward "self-healing" networks. These systems will not only detect a breach but will automatically reconfigure network segments to isolate the attacker and restore compromised services without human intervention. While this level of autonomy carries risks, the speed of modern attacks makes it a technical necessity. The goal for 2026 and beyond is to build resilient systems where AI agents act as the first line of defense, operating within a framework of strict governance and human-defined intent.