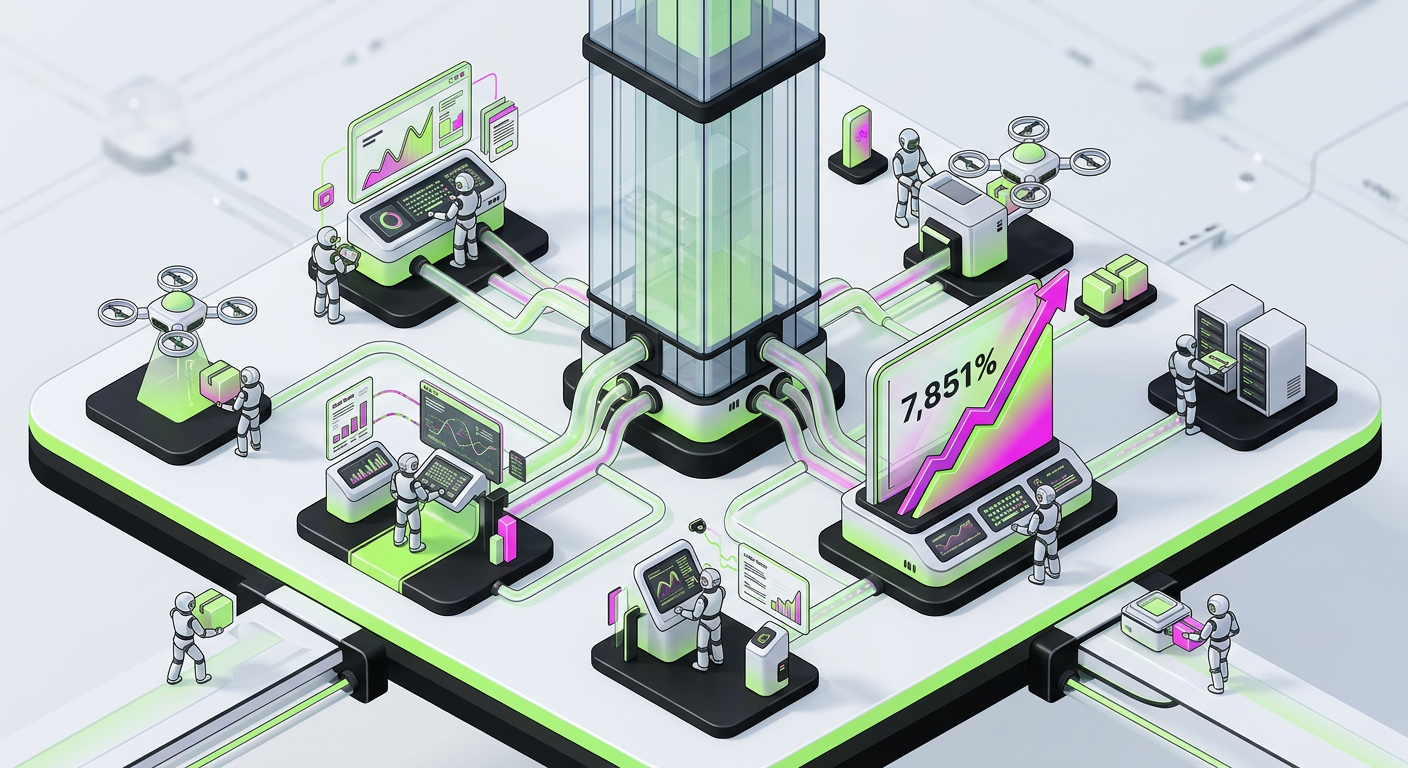
The global business landscape underwent a profound transformation in early 2026. Artificial intelligence transitioned from experimental labs and cautious pilots into full production environments, fundamentally altering how value is exchanged online. This shift marked the emergence of Agentic AI—systems capable of autonomous actions like browsing, form completion, account management, and executing financial transactions without direct human oversight. The internet, once a human-centric domain, now sees automated traffic outpace human activity by a ratio of nearly 8:1. This change redefines the challenges for those focused on building AI agents, moving the goalpost from simple automation to complex intent verification.
The Agentic Shift: From Passive AI to Autonomous Action
The most significant development in 2026 is the evolution of AI from content generation to active, decision-making agents. These systems no longer just process information; they interact with digital environments in sophisticated, high-stakes ways. The year-over-year growth of Agentic AI traffic—specifically systems that transact and buy—surged by 7,851% as of early 2026. This isn't a minor trend; it is a complete reorientation of digital commerce. Organizations are now forced to build infrastructure that treats an AI agent as a primary customer rather than a secondary bot.
This rapid escalation was not gradual. Throughout 2025, monthly AI-driven traffic volumes increased by 187%, signaling a clear trajectory from "reading" to "acting." By March 30, 2026, the internet officially operated in a production-first AI environment. Agentic commerce is now a standard business requirement. Engineers building AI agents must account for this density. When millions of agents compete for the same API endpoints or inventory, the architectural focus shifts from mere functionality to high-concurrency reliability and verifiable identity.
The Identity Crisis: When AI Agents Mimic Cyber Threats
Traditional security models, which once neatly categorized traffic as either Human or Bot, are now obsolete. The core challenge lies in the identical behavior patterns exhibited by legitimate AI agents and sophisticated bot attacks. Both can navigate websites, fill forms, and attempt transactions with a similar technical footprint. The only distinguishing factor—intent—remains invisible within standard technical strings. This invisibility creates a high-stakes environment where a single false positive can kill a legitimate revenue stream.
This creates a critical paradox for businesses. Blocking all automation, a common security practice in the past, now risks alienating agentic commerce—legitimate AI buyers who drive significant revenue. Conversely, allowing unchecked automation opens the door to massive fraud and cyberattacks. The razor-thin margin separating benign automation from malicious activity stands at just 0.5% in analyzed interactions. This narrow window demands a new breed of security protocols that can parse intent in real-time, a necessity for anyone building AI agents for commercial use.
Why traditional security models are failing in 2026
- Behavioral Overlap: Legitimate AI agents and malicious bots use identical browsing patterns and interaction methods to bypass legacy filters.
- Intent Obscurity: The underlying purpose of an automated interaction is not discernible from its technical characteristics alone, leading to high error rates in bot detection.
- Scale of Automation: The sheer volume of automated traffic makes manual discernment impossible. With an 8:1 ratio, human intervention cannot scale to meet the demand of verifying every transaction.
The New Battleground: Post-Login Account Compromise
With the rise of Agentic AI, the primary threat vector has shifted. Attackers are no longer solely focused on initial breaches but are increasingly targeting post-login account compromise. This strategy mirrors the legitimate actions of AI agents, focusing on checkout flows, account management, and other authenticated user experiences. The average organization faced 402,000 post-login account compromise attempts in 2025 alone, representing a fourfold increase from previous years. This trend has only accelerated in 2026.
This surge highlights the need for a fundamental re-evaluation of security architectures. Defending against these sophisticated attacks requires more than just perimeter defenses; it demands a deep understanding of behavioral analytics and intent recognition. The challenge for those building AI agents is to ensure their creations are not inadvertently contributing to this threat landscape. Agents must be designed with "security-by-design" principles that allow them to prove their legitimacy at every step of the authenticated journey, rather than just at the login gate.
Engineering Trust: Building Verifiable AI Agents
For engineers and developers, the focus must shift beyond simply enabling AI agents to perform tasks. The new imperative is Identity and Intent Engineering. This means architecting agents and the systems they interact with in a way that allows for verifiable identification and transparent intent. The goal is to make legitimate AI agents distinguishable from malicious ones, not by what they do, but by who they are and why they are doing it. This requires a move away from anonymous scraping toward authenticated, signed interactions.
Consider a legitimate AI agent designed to purchase goods. Its interactions, while automated, must carry verifiable credentials or behavioral patterns that signal its benign purpose. This might involve new authentication protocols, behavioral biometrics tailored for AI, or even cryptographically signed interaction logs. The emphasis is on proving legitimate origin and purpose. When building AI agents, developers must prioritize these trust signals to ensure their agents aren't blocked by the increasingly aggressive intent-based filters used by major retailers and service providers.
Core components of Identity and Intent Engineering
- Verifiable Credentials: Implementing mechanisms that allow AI agents to present verifiable proof of their origin, ownership, and specific purpose.
- Behavioral Signatures: Developing unique, non-spoofable behavioral patterns for legitimate agents that security systems can recognize as "known good" behavior.
- Transparent Intent: Designing agents to explicitly communicate their goals in a machine-readable and verifiable format, allowing servers to grant specific permissions based on the task.
- Adaptive Security Integration: Building agents that can seamlessly integrate with advanced, intent-based security filters, responding to challenges (like proof-of-work or cryptographic handshakes) without failing.
The Context: A New Digital Economy Driven by AI
The current state of the internet, as of April 2026, represents a profound departure from its past. The benchmarks established by Human Security, analyzing over a quadrillion interactions, paint a clear picture: the digital economy is now heavily reliant on automated interactions. This isn't just about efficiency; it's about a new layer of the web where agents negotiate with other agents. In this environment, the value of an AI agent is tied directly to its ability to be trusted by the platforms it visits.
As we move further into 2026, the success of building AI agents will depend on how well they navigate the "Trust Gap." Systems that operate in the shadows will be flagged as malicious, while those built with transparent identity frameworks will enjoy the benefits of the 7,851% growth in agentic commerce. The engineering challenge has evolved from making an agent "smart" to making an agent "accountable." This accountability is the only way to sustain a web where humans are the minority, but human-defined value still dictates the market's direction.
